A short story of Content Spoofing to HTML Injection in Apple using Dangling Markup Injection
Content Spoofing is an injection in which user input is reflected as it is in the application response which can be used in phishing attacks.
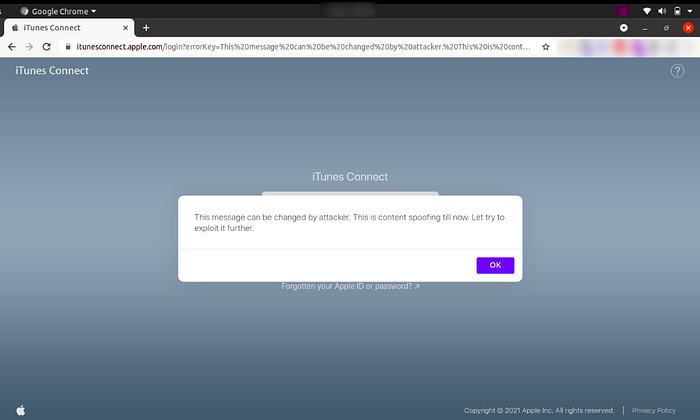
During the recon phase, I found itunesconnect.apple.com, a subdomain of apple and after digging into it, I had observed that the content of the error key parameter was reflecting back to the page as shown below
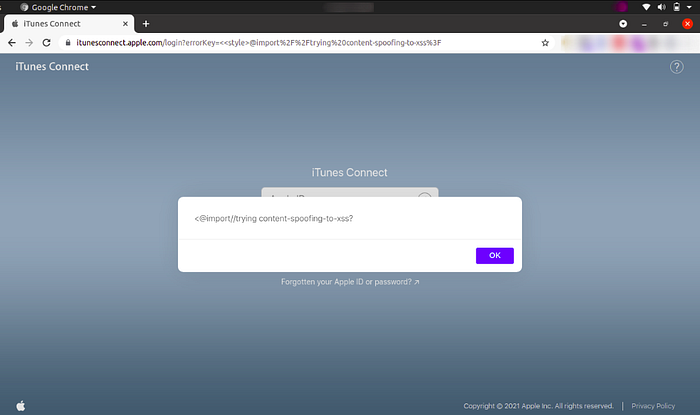
With normal inline Cross-Site Scripting(XSS) payloads, the application was giving a blank pop-up. After trying different scenarios, I have observed that dangling markup injection is possible on the vulnerable parameters (errorKey)
Let’s understand the concept of Dangling Markup Injection
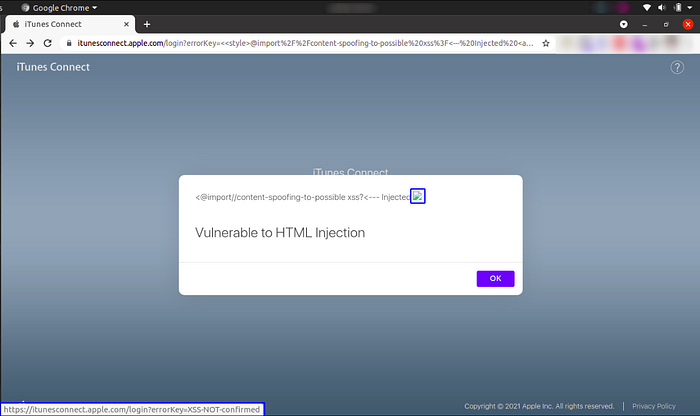
Dangling markup injection is very useful where we can’t find a way to execute our JavaScript due to input filters, content security policy, or other obstacles payloads but we can inject some HTML tags. It is used to steal the contents of the page without script by using resources such as images to send the data to a remote location that an attacker controls.
For our exploitation, I had used CSS @import as a payload. The main purpose of the @import method is to use multiple style sheets on a page.
Time for the final payload to have a broken image linked to itunesconnect.apple.com itself which led to HTML injection.
Reference:
https://rishuranjanofficial.medium.com/?p=3f8a898f21ee
Comments
Post a Comment